Recently several attacks have been in the news. As a result of this, I received various questions from people with regards to role assignments in their Azure environment:
Who exactly has which rights within my Azure environment?
At which level are permissions granted?
What about group memberships from which certain rights arise?
As some may already know, it is not that easy to answer these questions. Azure itself does not offer a solution at all to give you this insight.
That is why I started working on a script to provide insight into this, with the following requirements:
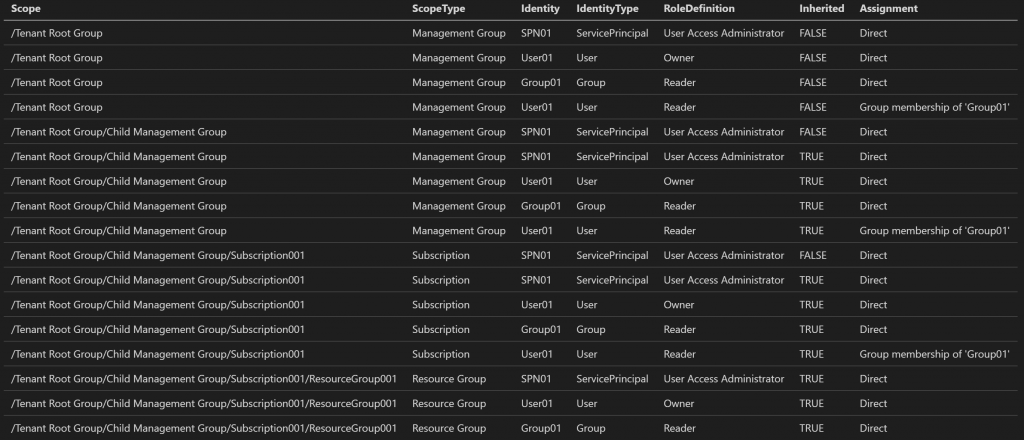
- Show parent-child relationships between different levels in the hierarchy (Management Groups, Subscriptions, Resource Groups and Resources)
- Be able to differentiate whether rights are configured at a particular level or whether they come from inheritance
- To whom are rights granted (users, groups and service principals)
- If there are rights that have been assigned to groups, who are the effective members of these groups?
- Which rights are exactly configured?
- Display the above data in both a flat and hierarchical structure
In the course of development, various other functionalities have also been added, which makes it just a little more flexible. For example, it is possible to skip certain levels in the hierarchy, ignore inherited permissions and not retrieve members of groups. It can take quite a while before all information is retrieved in a large environment, while gathering all data is not necessary in all cases.
The result has been published on GitHub: emilyvanputten/AzurePermissionInsight (github.com).
The script contains many elements that can be expanded and improved later. But for now, I want to share the current functionality so that everyone can take advantage of it. More details about its use, requirements and example output can be found in the readme on the GitHub repository.
If you run into bugs, miss certain data or have other suggestions, do not hesitate to contact me.